Zabbix - Networks and Applications Monitoring
AstLinux includes the Zabbix - zabbix_agentd and zabbix_proxy daemons. Zabbix is an enterprise-class open source software for monitoring of networks and applications, created by Alexei Vladishev. It is designed to monitor and track the status of various network services, servers, and other network hardware.
The zabbix_agentd and zabbix_proxy daemons (in AstLinux) are relatively small, headless, and efficient using the compiled 'C' language. Their purpose is to collect data and communicate upstream to the zabbix_server (not in AstLinux), which utilizes a production database and provides the web interface for reports and graphs.
The zabbix_server must be configured and maintained separately from AstLinux. A good starting point is the Zabbix Appliance which can be found on the Zabbix Downloads page. Installing the Zabbix Appliance in a Virtual Machine is a great way to learn Zabbix and possibly manage a small number of AstLinux boxes. Unfortunately, upgrading a Zabbix Appliance to a newer version is not as simple as it should be. Installing Zabbix from it's parts on a CentOS or Debian/Ubuntu distribution may be a better choice for some.
It should be clear that deploying a Zabbix monitoring solution is not for the solo AstLinux user. Though if you are responsible for many AstLinux boxes at many locations, configuring and maintaining Zabbix can be well worth the effort.
Note: AstLinux 1.0.5 or later is required
Note: AstLinux 1.3.3 or later includes Zabbix 3.0 LTS
Zabbix Version Compatibility
As with any client/server system, special attention must be given to what versions the clients and servers are running, and whether they are compatible. This is particularly true with Zabbix.
In general, the zabbix_agentd and zabbix_proxy daemons can properly associate with the same version series of zabbix_server or newer. The reverse is not generally true, as such the zabbix_agentd and zabbix_proxy daemons may not work with an older version of zabbix_server. For example a 2.0.x zabbix_agentd will work with a 2.2.x zabbix_server, but a 2.2.x zabbix_agentd will not work with a 2.0.x zabbix_server.
Tip -> Before upgrading AstLinux be sure to see if your zabbix_server version is in the same series or newer than what the latest AstLinux includes. You may need to first, migrate your zabbix_server to a newer version.
Note -> AstLinux 1.3.3 or later requires a zabbix_server using Zabbix 3.0 or later.
Be sure to check the Zabbix Documentation page for version specific details.
Zabbix Configuration
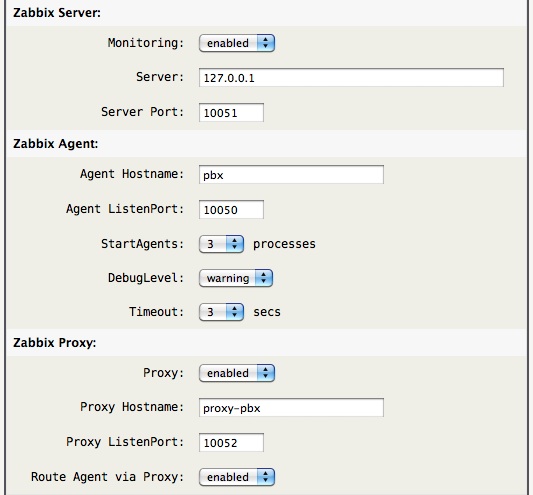
The AstLinux Web Interface is used for configuration, click on Configure Zabbix
Network tab → Network Services:

It is assumed the external zabbix_server is setup, configured and reachable by your AstLinux box.
When enabled, either only the “Zabbix Agent” (zabbix_agentd) is enabled or both the “Zabbix Agent” and “Zabbix Proxy” (zabbix_proxy) daemons are enabled.
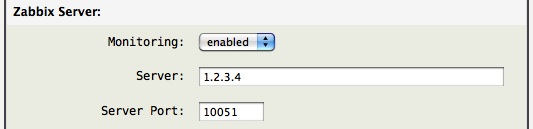
Replace the 1.2.3.4 Server address with your Zabbix server IP address or DNS name.
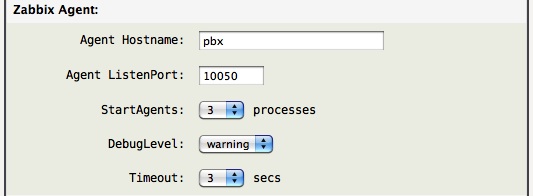
The zabbix_agentd daemon is configured to support both passive and active checks. The active check does not require any added firewall rules to a remote server since the connection is initiated outbound, zabbix_agentd → zabbix_server.
While passive checks are simpler for Zabbix to process, it requires a firewall rule “Pass EXT→Local 1.2.3.4 TCP 10050” to allow the Zabbix server at 1.2.3.4 to reach the zabbix_agentd service. As such, generally, active checks are used to reach zabbix_server so no additional firewall rules are needed.
Note -> The “Agent Hostname” entry must exactly match the configuration in the Zabbix server.
Advanced -> The auto-generated zabbix_agentd.conf file will “include” additional zabbix options if the file /mnt/kd/zabbix_agentd.userparams.conf exists.
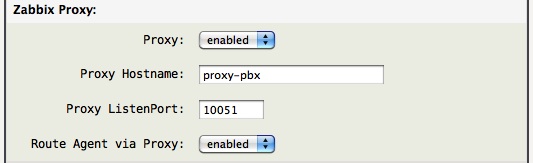
The “Zabbix Proxy” is optional.
The zabbix_proxy daemon does not require any added firewall rules to a remote server since the connection is initiated outbound, zabbix_proxy → zabbix_server.
The “Route Agent via Proxy” determines if the zabbix_agentd communicates in parallel with the zabbix_proxy to zabbix_server (disabled) or if the zabbix_agentd communicates directly with the local zabbix_proxy and only zabbix_proxy communicates with zabbix_server (enabled, the default).
Note -> The “Proxy Hostname” entry must exactly match the configuration in the Zabbix server.
Advanced -> The auto-generated zabbix_proxy.conf file will “include” additional zabbix options if the file /mnt/kd/zabbix_proxy.general.conf exists.
Encryption via Stunnel
Zabbix 3.0 or later supports encrypted communications between Zabbix server, Zabbix proxy and Zabbix agent using Transport Layer Security (TLS) protocol v.1.2. AstLinux 1.3.3 or later users may continue to use “stunnel” as outlined below, though new configurations should look at the native encryption support described here: Zabbix 3.0 Encryption
Earlier versions of Zabbix did not provide native support for encryption or certificate authentication for the zabbix_agentd or zabbix_proxy data streams. If the cleartext data that Zabbix exchanges with the server contains information that you don't want to share with the public internet, some sort of SSL wrapper is required. Using OpenVPN is one choice, but a simpler solution in this case is to use “stunnel”.
The example below demonstrates how to use stunnel to encrypt the zabbix_proxy connection to the Zabbix server, while the zabbix_agentd is also routed via the zabbix_proxy connection.
AstLinux - stunnel client config
STUNNEL_CLIENTS="127.0.0.1:10051~1.2.3.4~11612" #STUNNEL_CLIENT_CERT="/mnt/kd/ssl/zabbix-server-stunnel.pem"
Replace the 1.2.3.4 in STUNNEL_CLIENTS with your Zabbix server IP address or DNS name.
Optionally specify the zabbix-server-stunnel.pem cert/key file, uncomment the STUNNEL_CLIENT_CERT line. Without STUNNEL_CLIENT_CERT defined the stunnel connection is still encrypted, but no certificate identity checking is performed.
Zabbix server - stunnel server config
cert = /etc/stunnel/zabbix-server-stunnel.pem ... accept = 11612 connect = 127.0.0.1:10051
AstLinux Zabbix Configuration
Using the above stunnel configurations, the related AstLinux Zabbix settings are:
Zabbix Server: 127.0.0.1 Server Port: 10051 Proxy ListenPort: 10052 Route Agent via Proxy: [ enabled ]
Note -> The “Proxy ListenPort” must be set to 10052 so as to not conflict with the listening stunnel connection.
The resulting Zabbix Monitoring Configuration in the web interface: