Firewall External Block List
AstLinux provides an IPv4 / IPv6 Stateful Filtering Firewall, based on the excellent Arno's iptables Firewall (AIF) firewall script, developed by Arno van Amersfoort.
A feature of AIF (v2.0.1g or later) is the ability to parse *.netset text files for IP/Net entries and use the ipset command to generate a hashed list in kernel memory to allow a single iptables firewall rule to very quickly match incoming and/or outgoing traffic against this list. Equally important, this ipset list may be rebuilt and swapped into place without needing to totally rebuild the firewall rules.
This feature allows blocklists, often very large blocklists containing tens of thousands of IP/Net entries to be efficiently added and matched by an iptables rule forcing specific traffic to be dropped by the firewall.
Note: AstLinux 1.2.8 or later is required
Note: AstLinux 1.3.7 updated reload-blocklist-netset with asterisk, custom and customv6 netsets.
Note: AstLinux 1.4.4 updated reload-blocklist-netset with apiban netset.
Enable *.netset Blocklists
Select the Network Tab in the web interface.
Click on the Firewall Configuration:

Finally, check this entry under the “Block All Traffic by Host/CIDR:” section:
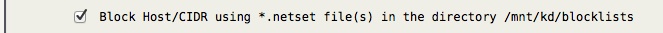
If you had previously enabled “Block Host/CIDR using the file /mnt/kd/blocked-hosts”, you will most likely want to migrate to a .netset file and no longer use /mnt/kd/blocked-hosts since the netset method loads much faster.
Updating *.netset Blocklists
AstLinux contains a command reload-blocklist-netset to regularly update .netset IP/Net entries.
From the CLI, issue the reload-blocklist-netset command without arguments to display usage and a list of supported external blocklist netsets.
Cron may be used to run this script once or twice every day, for example:
15 05,15 * * * reload-blocklist-netset /mnt/kd/blocklists firehol_level1 firehol_webclient >/dev/null 2>&1
Important -> Do not use the cron time schedule as above, make changes so the servers are not hit at the same time.
In this example, a /mnt/kd/blocklists/firehol_level1.netset and a /mnt/kd/blocklists/firehol_webclient.netset file will be created.
Tip -> You must manually create the /mnt/kd/blocklists directory if it does not exist.
If you are manually adding or deleting any .netset files you can apply the changes to the firewall with this command from the CLI:
arno-iptables-firewall force-reload
Note: AstLinux 1.3.7 or later adds support for new netsets: asterisk, custom and customv6.
asterisk → Aggregate multiple Asterisk/SIP/VoIP blacklists, including blocklist_de_sip.
custom → Use variable BLOCKLIST_CUSTOM_URLS containing one or more (space/newline separated) URLs.
customv6 → Use variable BLOCKLIST_CUSTOMV6_URLS containing one or more (space/newline separated) URLs.
Tip -> The custom netset will use iprange to aggregate IPs and look up DNS if needed.
For example, you can create you own custom blocklist using abuse.ch blocklists:
# 'custom' Blocklist by https://abuse.ch/ BLOCKLIST_CUSTOM_URLS=" https://feodotracker.abuse.ch/downloads/ipblocklist.txt https://sslbl.abuse.ch/blacklist/sslipblacklist.txt "
Warning -> Don't miss the closing double-quote.
This variable can be added directly into the /mnt/kd/rc.conf.d/user.conf file, or edited via the Network tab → Advanced Configuration: User System Variables.
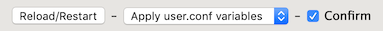
In order to apply user.conf settings changes, using the Edit tab:
Or use the CLI command:
gen-rc-conf
Note: AstLinux 1.4.4 or later adds support for a new netset: apiban.
apiban → REST API for sharing IP addresses sending unwanted SIP traffic. Requires an API Key via https://apiban.org/.
After receiving your API Key via email, copy it to a newly created /mnt/kd/apiban.conf file.
File format for *.netset Files
Each .netset file may contain only one IP/Net entry per line, each IP/Net entry must start at
the beginning of the line and any valid entry must be immediately followed by a new-line or a POSIX :space: character. File contents not matching an IP/Net will be ignored.
File naming convention, use *v6.netset files for IPv6 entries, all other *.netset files default to IPv4. Filenames are limited to a maximum of 27 characters before the .netset suffix.
Note -> The filename prefix is used as the ipset set name, the Linux Kernel limits the set name length.
Optional whitelist.netset, whitelistv6.netset files may contain IP/Net entries that will not be blocked by any other *.netset file. Automatically by default,
all Private (RFC1918), Link-Local and Multicast IP/Nets will be whitelisted, even if whitelist netset files are not defined.
Note -> Whitelist IP/Net entries are not necessarily “allowed” in the firewall, their scope only keeps other *.netset files from blocking specific traffic.
Web Interface Edit tab
Special *.netset files will be displayed in the Edit tab “System Configuration” file list if they exist.
Blocklist IPv4 Set: blocked-hosts.netset
Blocklist IPv6 Set: blocked-hostsv6.netset
Whitelist IPv4 Set: whitelist.netset
Whitelist IPv6 Set: whitelistv6.netset
External sources for Blocklists
The “firehol_level1” blacklist is composed from aggregating IP lists, providing maximum protection with minimum false positives.
Tip -> The “firehol_level2” and/or “firehol_level3” blacklist may be used in addition to the base “firehol_level1” blacklist.
FireHOL IP Lists
The “voipbl” distributed VoIP blacklist is aimed to protect against VoIP Fraud and minimizing PBX network abuse. (Dec 2018, not maintained very well anymore, many false positives)
VoIP Blacklist
Spamhaus DROP and EDROP are included in the “firehol_level1” blocklist.
Spamhaus Don't Route Or Peer Lists
Aggregate your own custom blocklist using FireHOL's update-ipsets on a server external to AstLinux.
Using update-ipsets